Google Simplifies 2-Factor Authentication Setup
09.05.2024
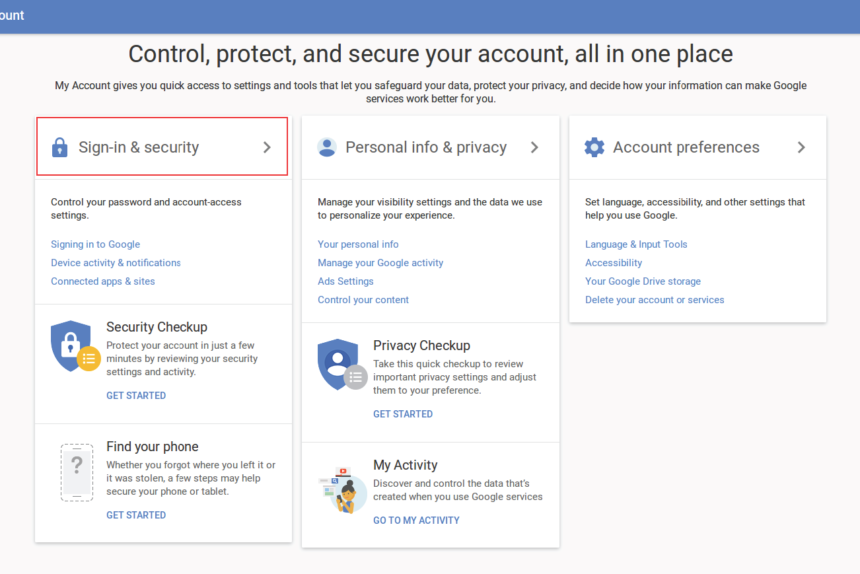
Google announced on Monday that it’s streamlining the process of activating two-factor authentication (2FA) for users with personal and Workspace accounts.
Also known as 2-Step Verification (2SV), this security measure adds an extra layer of protection to users’ accounts to prevent unauthorized access in case passwords are compromised.
The update involves adding a second authentication method, such as an authenticator app or a hardware security key, before enabling 2FA, thereby eliminating the need for less secure SMS-based authentication.
“This is especially beneficial for organizations utilizing Google Authenticator (or similar time-based one-time password (TOTP) apps),” the company stated. “Previously, users were required to enable 2SV with a phone number before being able to add Authenticator.”
Users with hardware security keys have two options for adding them to their accounts: registering a FIDO1 credential on the hardware key or assigning a passkey (i.e., a FIDO2 credential) to it.
Regarding Workspace accounts, users may still need to enter their passwords alongside their passkeys if the admin policy for “Allow users to skip passwords at sign-in by using passkeys” is disabled.
In another update, users who choose to disable 2FA from their account settings will no longer have their enrolled second steps automatically removed.
“When an administrator disables 2SV for a user from the Admin console or via the Admin SDK, the second factors will be removed as usual, ensuring user off-boarding workflows remain unaffected,” Google explained.
This development comes as Google reported that over the past year, more than 400 million Google accounts have adopted passkeys for passwordless authentication.