DDoS Attacks on the Environmental Services Industry Surge by 61,839% in 2023
15.01.2024
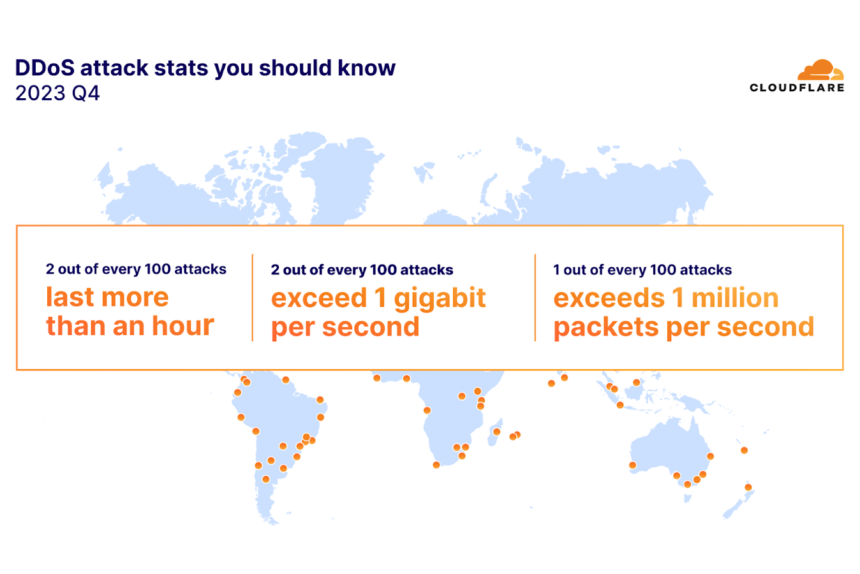
During the fourth quarter of 2023, the environmental services industry experienced an unprecedented surge in HTTP-based distributed denial-of-service (DDoS) attacks, constituting 50% of its HTTP traffic. This represents an alarming year-over-year increase of 61,839%, as reported by web infrastructure and security company Cloudflare in its DDoS threat report. This surge in cyber attacks coincided with COP 28, held from November 30th to December 12th, 2023, indicating a disturbing trend in the cyber threat landscape.
The rise in HTTP attacks targeting environmental services websites follows a recurring pattern observed annually during environmental conferences like COP 26 and COP 27, as well as other United Nations environment-related events. This trend highlights the growing intersection between environmental issues and cybersecurity, becoming a focal point for attackers in the digital age.
Despite the environmental services sector being a new target in Q4 2023, the cryptocurrency industry remains the primary casualty in terms of HTTP DDoS attack volume. The cryptocurrency industry faced over 330 billion HTTP requests, constituting more than 4% of all HTTP DDoS traffic for the quarter. Gaming, gambling, and telecommunications industries emerged as the second and third most attacked sectors.
The U.S. and China stand out as the main sources of HTTP DDoS attack traffic, with the U.S. maintaining its position as the largest source for five consecutive quarters since Q4 2022. Together, China and the U.S. contribute to over a quarter of all global HTTP DDoS attack traffic, followed by Brazil, Germany, Indonesia, and Argentina, accounting for the next 25%.
These developments occurred amid a significant increase in DDoS attacks targeting Palestinian banking, information technology, and internet platforms during the Israel-Hamas War and Operation Iron Swords. The percentage of DDoS attack traffic targeting Palestinian websites grew by 1,126% quarter-over-quarter. Additionally, DDoS attacks targeting Taiwan experienced a 3,370% growth amid the Taiwanese presidential elections and rising tensions with China.
Akamai’s retrospective on DDoS trends in 2023 also revealed that DDoS attacks became more frequent, longer, highly sophisticated (with multiple vectors), and focused on horizontal targets, attacking multiple IP destinations in the same event. Cloudflare’s report highlighted the increasing threat posed by unmanaged or unsecured API endpoints, with HTTP anomalies being common signals of malicious API requests. More than half (51.6%) of traffic errors from API origins comprised ‘429’ error codes, indicating ‘Too Many Requests.’